The final weeks of December are often quieter for many businesses—but that doesn’t mean cyber risk slows down. In fact, threat actors frequently take advantage of year-end distractions, reduced staffing, and delayed maintenance.
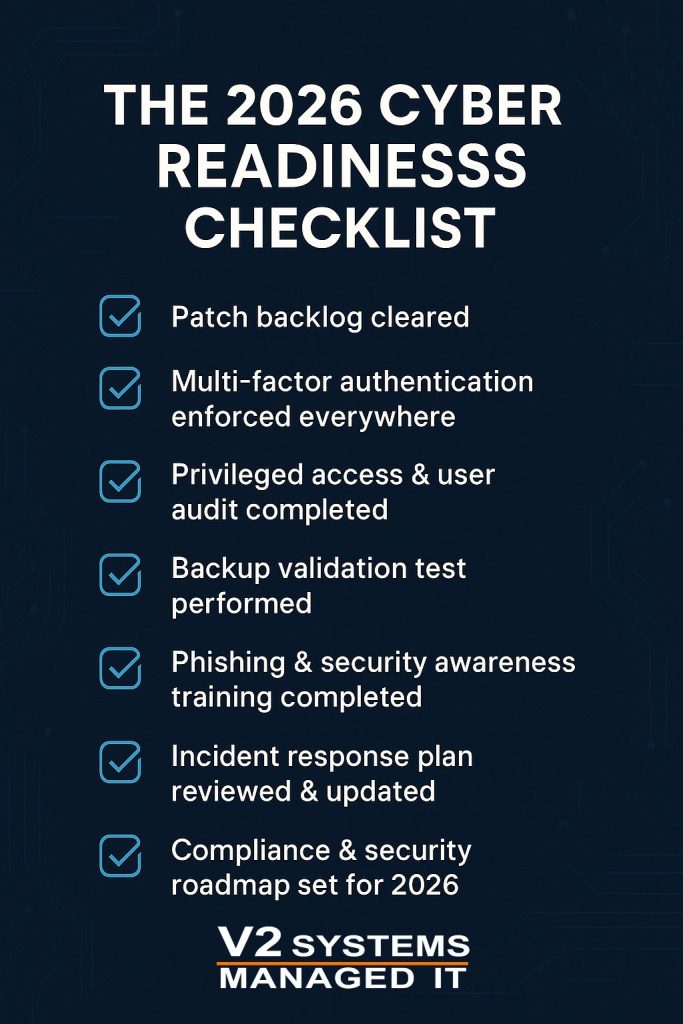
Before turning the calendar to 2026, now is the ideal time to pause, assess, and ensure your organization has covered the cybersecurity basics. This 2026 Cyber Readiness Checklist outlines the critical steps every business—government contractors and SMBs alike—should complete before January 1.
✅ The 2026 Cyber Readiness Checklist
1. Patch Backlog Cleared
Unpatched systems remain one of the most common entry points for attackers. Before year-end, ensure all operating systems, applications, and network devices are fully updated—and that no critical patches are lingering.
For government contractors, this is especially important as patching ties directly into CMMC and DFARS requirements.
2. Multi-Factor Authentication (MFA) Enforced Everywhere
If MFA isn’t enabled across all remote access, email, cloud platforms, and privileged accounts, it should be before January 1. Credential-based attacks continue to rise, and MFA remains one of the most effective defenses.
3. Privileged Access & User Audit Completed
Year-end is the perfect time to review who has access to what. Remove unnecessary admin privileges, disable dormant accounts, and verify that access aligns with job roles—especially after employee changes throughout the year.
This step is critical for both zero trust security and CMMC alignment.
4. Backup Validation Test Performed
Backups are only useful if they work. Before the holidays:
-
Verify backups are running successfully
-
Perform a test restore
-
Confirm backup data is protected from ransomware
5. Phishing & Security Awareness Training Completed
Human error continues to be a leading cause of breaches. Completing phishing training and awareness refreshers before the end of the year helps reduce risk during holiday travel and PTO-heavy weeks.
6. Incident Response Plan Reviewed & Updated
If a cyber incident occurred tomorrow, would your team know exactly what to do?
Before January:
-
Review escalation paths
-
Validate contact lists
-
Ensure leadership roles are clearly defined
-
Test tabletop or response scenarios
7. Compliance & Security Roadmap Set for 2026
Finally, businesses should document what compliance and security initiatives lie ahead in 2026, such as:
-
CMMC preparation or certification timelines
-
Cyber insurance requirement changes
-
Hardware refresh or Windows 10 end-of-life planning
-
Security tool or monitoring upgrades
How V2 Systems Helps Businesses Start 2026 Securely
At V2 Systems, we help organizations move into the new year with clarity—not guesswork. Our team supports:
-
Managed IT and cybersecurity services
-
Proactive patching, monitoring, and backups
-
Security awareness training
-
Compliance readiness for CMMC, DFARS, and cyber insurance
-
Clear, predictable pricing and long-term planning
For government contractors, we also work with trusted partners like Rimstorm to support secure enclave environments and CMMC readiness.
Conclusion: Finish Strong, Start Secure
Completing this checklist before January 1 helps ensure your business enters 2026 with fewer vulnerabilities, stronger defenses, and a clear security roadmap. Whether you’re a small business or a government contractor, preparation now can prevent costly incidents later.
👉 Contact V2 Systems today for a complimentary two-hour consultation and start 2026 with confidence.